Present Blog – IT Thought Leadership
Blog Present-IT thought leadership
Blog Present-IT thought leadership
IT thought leadership blog for CIOs and CTOs in Canada seeking resources to drive IT as a business contributor: hybrid cloud, infrastructure, managed services and security and IT recruitment.
 It is no longer just those in IT or business owners concerned about the security of their data that need to have a solid foundation in cybersecurity language. All employees should have an understanding of the most commonly used terms in IT security so they will be better equipped to protect themselves and the company they work for from cyberattacks.
It is no longer just those in IT or business owners concerned about the security of their data that need to have a solid foundation in cybersecurity language. All employees should have an understanding of the most commonly used terms in IT security so they will be better equipped to protect themselves and the company they work for from cyberattacks.
However, many employees are still unfamiliar with many cybersecurity terms, and it is not made easy by all the abbreviations used. So, in this blog article we look at the definition of 15 terms we believe everyone should know.
Ransomware
A form of malware that deliberately prevents you from accessing files on your computer – holding your data hostage. It will typically encrypt files and request that a ransom be paid in order to have them decrypted or recovered.
MFA (Multi-factor authentication
The goal of multi-factor authentication is to create an additional layer of defense beyond just using a password. MFA is a security technology that requires at least two independent pieces of information (2FA) to verify a user's identity when attempting to log in or access a resource.
EDR (Endpoint detection and response)
An EDR is designed to provide continuous detection and response to endpoints (workstations, laptops, servers) against malware and threats and thus provide anti-ransomware capabilities.
EDR comes with a set of behavioral detection rules and supports custom rule mechanisms in addition to providing AI-based detection to counter emerging threats.
SIEM (Security Information and Event Management)
The main purpose of a SIEM is to provide information by collecting event logs (syslogs). A SIEM aggregates data across your business from a variety of sources, including endpoints, web applications, physical and virtual servers, and network devices, allowing millions of events to be viewed in seconds.
It also generates high-context alerts, allowing you to perform actions that reduce the vulnerability of your environments.
Social engineering
This is a technique used to manipulate and deceive people to gain sensitive and private information or access. Scams based on social engineering tend to lure unsuspecting users into exposing data, spreading malware infections, or giving access to restricted systems.
Phishing
It is a type of social engineering scheme that involves defrauding people using an app or a website that impersonates a trustworthy or often well-known business in an attempt to obtain confidential information. When you receive an email from Microsoft saying you need to update your password, don’t take it at face value — always verify the source first.
Malware
Malware is an umbrella term that describes all forms of malicious software designed to wreak havoc on a computer. Common forms include viruses, trojans, worms and ransomware.
These malicious programs can perform a variety of functions, including stealing, encrypting or deleting sensitive data, altering or hijacking core computing functions and monitoring users' computer activity without their permission.
Bot/Botnet
A type of software application or script that performs tasks on command, allowing an attacker to take complete control remotely of an affected computer. A collection of these infected computers is known as a “botnet” and is controlled by the hacker or “bot-herder”.
Spyware
A type of malware that functions by spying on user activity without their knowledge. The capabilities include activity monitoring, collecting keystrokes, data harvesting (account information, logins, financial data), and more.
Worm
A piece of malware that can replicate itself in order to spread the infection to other connected computers.
DoS and DDoS Attacks
A denial-of-service attack (DoS attack) is a cyber-attack where the perpetrator seeks to make a resource unavailable to its intended users by flooding it with requests.
In a distributed-denial-of-service attack (DDoS attack) the incoming traffic flooding the victim originates from many different sources. This effectively makes it impossible to stop the attack simply by blocking a single source.
Zero-day attacks
When a vulnerability is found within a piece of software, vendors will release an update to fix the gap in security. However, cyberattackers can release a piece of malware that exploits the security vulnerability before software developers can address it. This is known as a zero-day attack.
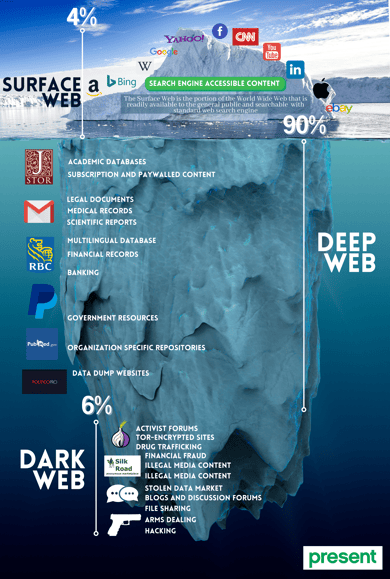
Dark Web
The dark web is a part of the World Wide Web that’s only accessible by installing special software and is used for more sinister purposes. It allows users to access an encrypted network where users and operators remain anonymous and untraceable. Because it’s so hidden, this is a haven for illegal activities.
Pen Testing
Short for Penetration testing, this is the practice of testing a computer system or network to find vulnerabilities that cybercriminals could exploit. The main objective of pen testing is to determine security weaknesses.
Bill 64
For those located in Quebec, it is a term we are hearing more and more about. Bill 64 is an Act to modernize legislative provisions in regard to the protection of personal information. It creates obligations on private and public sector organizations in Quebec similar to those imposed by the GDPR in Europe. The first deadline is coming into affect on September 21, 2022. Read more here.
For more information on Present’s IT security offering, visit our website and request a meeting with one of our security experts by clicking on the link below.
About Blog
The right use of technology addresses business challenges and drives business growth in all areas of an enterprise. We hope this blog will offer insight into developing strategies and tactics to enable you to identify those key drivers of growth and keep pace with and anticipate the rapid technology change of today.
Posts by Topic
- IT infrastructure (118)
- IT security (95)
- IT Innovation (59)
- Trends (51)
- Cloud (48)
- Managed services (48)
- Mobility (38)
- CIO/IT leaders (29)
- Digital transformation (29)
- Events (28)
- News (23)
- Microsoft 365 (17)
- Security (17)
- IBM (16)
- Disaster recovery (DR) (14)
- High availability (12)
- Recruitment (12)
- Storage (12)
- Big Data (11)
- Collaboration (11)
- AI (10)
- Case study (9)
- Office 365 (9)
- BYOD (8)
- Customer Experience (8)
- Hybrid Cloud (7)
- Current events (6)
- SAP Hana (5)
- Business intelligence (BI) (4)
- Converged infrastructure (4)
- Convergence / Hyper-convergence (4)
- Virtualization (4)
- Copilot (3)
- Future of retail (2)
- Retail (2)
- trend (2)
- Backups (1)
- Beacon (1)
- Blog Migrations (1)
- Contests (1)
- Infrastructure TI (1)
- Innovation TI (1)
- IoT (1)
- MDM (1)
- Stockage (1)
- Virtualisation (1)
- blockchain (1)
- cio (1)
- replication (1)
- Étude de cas (1)

