Present Blog – IT Thought Leadership
Blog Present-IT thought leadership
Blog Present-IT thought leadership
IT thought leadership blog for CIOs and CTOs in Canada seeking resources to drive IT as a business contributor: hybrid cloud, infrastructure, managed services and security and IT recruitment.
How confident are you that you can identify a phishing scam?
Jennifer Bridgeman_ Would you fall for a social engineering tactic? It’s harder than you think to identify them.
Would you fall for a social engineering tactic? It’s harder than you think to identify them.
Attacks against enterprises and SMBs using social engineering are not only growing more frequent, but they're also increasingly more sophisticated. Enterprises must exercise due diligence in order to keep one step ahead of cybercriminals since they are coming up with even more clever ways to trick people into handing over valuable company data.
What is Social Engineering?
Social engineering is the term used for a broad range of malicious activities used by cybercriminals to trick users into making security mistakes or giving away sensitive information.
Any successful cyber-attack that employs social engineering preys on one basic human instinct: trust. According to the 2022 Verizon Data Breach Investigations Report, 82% of breaches involve the human element, whether that be through pretexting, phishing or use of stolen credentials.
All it takes is one email, phone call, or text message that appears to be coming from a recognized person or organization to fall through the cracks. After the deception works and the attack succeeds, the cybercriminals can expose sensitive information, use it to their benefit, or take control of corporate devices, systems and networks.
I would never fall for that!
Suspicious links are so common online that most of us are uneasy about clicking on any links in almost any situation.
You may be thinking, “Surely this can’t still be happening.” Dilbert portrays it best:
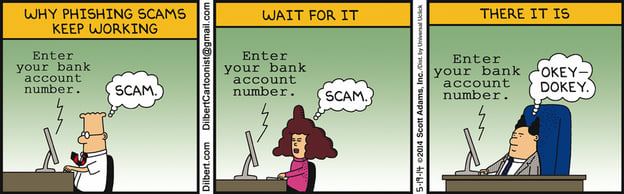
Three billion fraudulent emails are sent out every day to try to compromise sensitive information. And, according to the 2021 edition of Terranova Security’s Phishing Benchmark Global Report, 19.8% of total participants click on the phishing email links.
How good are you at spotting when you’re being pushed?
It can be harder than you think. Try this quiz to see if you can tell what’s fake and what’s real.
Why does social engineering work?
Social engineering is so effective and dangerous because people make mistakes.
Successful social engineering scams rely on that knee-jerk human reaction to trust the sender and believe the message. Being busy, not paying close enough attention or complacency can lead to users being too trustful.
The best examples of social engineering are the ones that play all the right notes on a victim’s emotional scale. The social engineering attacks prey on human emotion whether that be fear, greed, curiosity or helpfulness.
How to Spot Common Social Engineering Tactics
Everyone within an organization must know what social engineering attacks look and/or sound like. Otherwise, the risk of data or system exposure through a malicious email link or attachment can increase significantly.
Let us take a closer look at the various forms that cybercriminals can use to package their social engineering attempts.
Phishing
Phishing encompasses a wide range of devious tactics, including deceptive emails, fake websites, and misleading text messages. They all have the same goal: to steal confidential data belonging to an individual or organization. Phishing attacks are typically successful when they appear to come from a well-known source, trusted acquaintance or organizational entities.
Pretexting
Pretexting is a social engineering technique where a false identity dupes a victim into giving up sensitive information. For instance, a cybercriminal may know that the targeted individual recently bought an item from Apple and pretends to be a company customer service representative to acquire credit card information or other confidential details.
Quid Pro Quo
Quid pro quo scams rely on an exchange of information to convince a victim to act. Often, they offer to provide a service in exchange for a benefit. A common tactic in this category is when a cybercriminal impersonates an IT support employee and call victims who recently opened a support ticket, promising to fix a virus-related issue if they are provided with login credentials.
Spear Phishing
Spear phishing is a cybercrime that deploys targeted attacks against individuals and businesses using relevant and well-crafted messages. Hackers will collect details about the targeted parties and, using email, use that information to appear familiar to the victim.. Though often used simply to steal user data, spear phishing can also be a means to install malware or ransomware onto someone’s device.
Vishing
Vishing uses phone calls or voicemail to convince victims that they need to act quickly. Typically, messages will dangle the threat of being subjected to legal action or a criminal attack, such as one urging the victim to reset their banking information because their account has been hacked.
Water-Holing
Water-holing targets a group of users and websites they frequent. The cybercriminal looks for a security vulnerability in one of these websites and then infects it with malware. Eventually, a member of the targeted group will be victimized by the malware. This specific social engineering technique is also very hard to detect.
Baiting
Baiting is both an online and physical social engineering attack that promises the victim something in exchange for an action. This can include plugging in a USB key or downloading an attachment to receive free movie downloads for life. The computer and the network can be targets of malicious software that captures login credentials or sends fake email messages.
Malware Removal
The promise of malware removal messages tricks victims into paying for a tool to remove viruses or other nefarious software from their devices. Depending on the scam, the criminal can steal the victim’s credit card information or install a different malware or ransomware program onto the computer or mobile device. Keep an eye out for malware emails – nearly 95% of payloads are delivered this way.
The reality is that people keep falling for these social engineering attacks. That why attackers keep doing them as they work! Their methods are constantly evolving so the ones we see today are sure to evolve. Hence the importance of continually educating your employees. Training and testing them should be a part of your cybersecurity plan.
Present partners with Terranova Security, a Gartner magic quadrant leader, to offer a high-quality customizable training program. Contact one of our cybersecurity experts to learn more!
About Blog
The right use of technology addresses business challenges and drives business growth in all areas of an enterprise. We hope this blog will offer insight into developing strategies and tactics to enable you to identify those key drivers of growth and keep pace with and anticipate the rapid technology change of today.
Posts by Topic
- IT infrastructure (118)
- IT security (95)
- IT Innovation (59)
- Trends (51)
- Cloud (48)
- Managed services (48)
- Mobility (38)
- CIO/IT leaders (29)
- Digital transformation (29)
- Events (28)
- News (23)
- Microsoft 365 (17)
- Security (17)
- IBM (16)
- Disaster recovery (DR) (14)
- High availability (12)
- Recruitment (12)
- Storage (12)
- Big Data (11)
- Collaboration (11)
- AI (10)
- Case study (9)
- Office 365 (9)
- BYOD (8)
- Customer Experience (8)
- Hybrid Cloud (7)
- Current events (6)
- SAP Hana (5)
- Business intelligence (BI) (4)
- Converged infrastructure (4)
- Convergence / Hyper-convergence (4)
- Virtualization (4)
- Copilot (3)
- Future of retail (2)
- Retail (2)
- trend (2)
- Backups (1)
- Beacon (1)
- Blog Migrations (1)
- Contests (1)
- Infrastructure TI (1)
- Innovation TI (1)
- IoT (1)
- MDM (1)
- Stockage (1)
- Virtualisation (1)
- blockchain (1)
- cio (1)
- replication (1)
- Étude de cas (1)