Present Blog – IT Thought Leadership
Blog Present-IT thought leadership
Blog Present-IT thought leadership
IT thought leadership blog for CIOs and CTOs in Canada seeking resources to drive IT as a business contributor: hybrid cloud, infrastructure, managed services and security and IT recruitment.
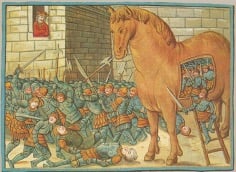
A model inherited from the past: Trust but verify
"Doveryai, No Proveryai" ("Trust but verify") is a Russian proverb, which became the catch phrase of Ronald Reagan during his nuclear disarmament negotiations with Mikhail Gorbachev.
It was not so long ago that all resources and users were inside the network perimeter. Network security, and an antivirus on endpoints, were pretty much everything we needed.
The cunning Ulysses has already demonstrated the limits of this approach.
The new reality
But today, the Internet has transformed the way of running our business.
- Now, our users are employees, but also partners and subcontractors, some of which use their own devices.
- We work remotely and access corporate resources or those of our customers and suppliers from our corporate laptop or our own workstation.
- We store sensitive data in the cloud.
- We deploy devices connected to our supply chains, our fields, our factories and our buildings.
The old security model can no longer meet the new data protection requirements.
For example:
- When cybercriminals compromise an endpoint in a perimeter, they can move laterally to extract sensitive data.
- Phishing attacks and identification theft enable attackers to use the identity of the users and access their data.
We live in a new reality and we can no longer believe that everything that happens behind the business firewall is safe.
Zero Trust
This is where the Zero Trust model comes in.
It has been more than a decade since Jon Kindervag, then at Forrester, founded the concept "Never trust, always verify". Like Joseph Stalin who would have said "I trust noone, not even myself".
This approach was adopted by all IT industry players including Microsoft, the NIST, Google and Fortinet.
Why should you adopt this model today?
Zero Trust represents a must-see change in the security strategy in order to adequately meet major changes in:
- Assets to be protected.
- The evolution of attack techniques.
- Disastrous consequences of cyber-attacks such as ransomwares.
What does it involve?
The Zero Trust concept includes the following three principles:
- All resources must be accessible in a secure way, from a secure machine, regardless of the location.
- Access control is based on the "need to know" correlated with the identity of a user and what this user is allowed to access.
- Essentially, a zero-trust security approach assumes that each network has undergone a breach, each machine is compromised, and each user is at risk. It is therefore necessary to save and analyze information for verification purposes.
What is the plan of action?
Zero Trust is both a model, a state of mind and a plan of action. And as such the roadmap is specific to your company.
You should aim, in stages to:
- Decrease your exposure on the following attack surfaces:
- Identification: Improve authentication (multi-factor authentication, conditional access)
- Devices: Put in place an advanced detection and response type protection, control applications with intune and optimize device management.
- Applications: Guarantee appropriate applications permissions, control access and monitor abnormal behaviors.
- Networks: Limit access with network segmentation and limiting lateral movements, keeping unauthorized resources out.
- Data: Check data access and secure data flows.
- Improve our security operations by taking advantage of a S.I.E.M.
So where to start?
Of course you should always start by identifying your vulnerabilities through audits, then after analysis and depending on your risk tolerance, determine your action plan and its steps in order of priority.
It is obvious, however, that the urgency is to secure identities and devices since these two surfaces are today the most attacked and constitute your greatest risks.
At this very moment, cybercriminals take advantage of your outdated defense by capitalizing on the vulnerabilities of your systems.
So that's where you should start, since the implementation of these two measures will provide you with the greatest value for a minimal investment.
Emergency measures
These two measures should be put in place immediately.
- Deploy multi-factor authentication for Internet-connected systems, such as e-mail, remote desktop and VPN.
- Protect your endpoints with a behavior-based advanced threat and defense detection solution.
Once these two leaks are sealed, you will have time to establish a more expanded roadmap.
Contact us without delay for a conversation with one of our security specialists.
We also invite you to consult the following articles and subscribe to our blog.
https://blog.present.ca/5-deadly-myths-for-small-business-security
https://blog.present.ca/present-just-saved-another-client-from-a-cyberattack
https://blog.present.ca/how-to-recover-from-a-ransomware-attack
About Blog
The right use of technology addresses business challenges and drives business growth in all areas of an enterprise. We hope this blog will offer insight into developing strategies and tactics to enable you to identify those key drivers of growth and keep pace with and anticipate the rapid technology change of today.
Posts by Topic
- IT infrastructure (118)
- IT security (97)
- IT Innovation (59)
- Trends (51)
- Cloud (48)
- Managed services (48)
- Mobility (38)
- CIO/IT leaders (29)
- Digital transformation (29)
- Events (28)
- News (23)
- Microsoft 365 (17)
- Security (17)
- IBM (16)
- Disaster recovery (DR) (15)
- High availability (12)
- Recruitment (12)
- Storage (12)
- Big Data (11)
- Collaboration (11)
- AI (10)
- Case study (9)
- Office 365 (9)
- BYOD (8)
- Customer Experience (8)
- Hybrid Cloud (7)
- Current events (6)
- SAP Hana (5)
- Business intelligence (BI) (4)
- Converged infrastructure (4)
- Convergence / Hyper-convergence (4)
- Virtualization (4)
- Copilot (3)
- Backups (2)
- Future of retail (2)
- Retail (2)
- trend (2)
- Beacon (1)
- Blog Migrations (1)
- Contests (1)
- Infrastructure TI (1)
- Innovation TI (1)
- IoT (1)
- MDM (1)
- Stockage (1)
- Virtualisation (1)
- blockchain (1)
- cio (1)
- replication (1)
- Étude de cas (1)