Present Blog – IT Thought Leadership
Blog Present-IT thought leadership
Blog Present-IT thought leadership
IT thought leadership blog for CIOs and CTOs in Canada seeking resources to drive IT as a business contributor: hybrid cloud, infrastructure, managed services and security and IT recruitment.
RecoverPoint: accessible and reliable solution for disaster recovery
present
A recent survey of thousands of companies worldwide, to develop a detailed picture of the situation in terms of data protection was concluded and raised disturbing findings.
In Canada, 66 % of companies say they have little confidence in their disaster recovery capabilities. It is a well-founded fear, because the data protection investment usually does not follow the constant evolution of storage solutions.
If we consider that in 2014, in Canada, the average cost of disaster recovery was $ 1.8 million, it is essential to consolidate protection and business objectives, to avoid such a catastrophic situation.
Combine business strategy and data protection
1. Determine risk tolerance in case of disaster
Companys must know their resistance to minor disasters and major disasters to measure:
- • its RPO (RecoveryPoint Objective): tolerance to data loss;
- • its RTO (Recovery Time Objective): tolerance to loss of service time.
These factors are critical because once identified, tested and secured to the business objectives of the company, they can justify emergency IT investment
2. Establish the hierarchy of availability requirements
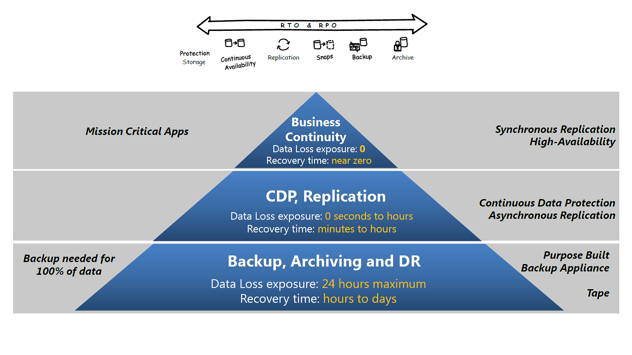
You must then develop a recovery plan tailored to the types of disaster or outages that may occur, considering its IT environment in a pyramid shape.
1) Bottom (Back Up-Archiving and DR)
To be used in case of major disaster causing the interruption of all services. This is the recovery system to be used when necessary to recover 100% of the company's data.
- • RPO: 24 hours’ maximum
- • RTO: a few hours to a few days
2) The center (Continuous protection of data)
Collect 10% of a company's applications. These applications are continuously protected through asynchronous replication.
- • RPO: zero seconds to hours
- • RTO: minutes to hours
3) The top (Business Continuity)
Applies one or two of the company's most critical applications. There the data is highly available thanks to synchronous replication system that ensures the protection of the most necessary data to the maintenance of a company's activities.
- • RPO: zero seconds
- • RTO: near zero
This type of architecture requires the use of a continuous data protection solution (CDP), which reverts to the exact moment prior to the breakdown of services and provides excellent resistance to disasters.
However, although this solution has existed for numerous years, very few companies are using it, because it has long been considered too expensive. Fortunately, virtualization with its increasingly widespread infrastructure changes everything ...
Virtualization helps backup data protection
Less than two years ago, most companies were only 50 or 60% virtualized and most critical data was stored on physical devices. Installing a CDP therefore represented a considerable investment of both material and human resources.
Today, with enterprises being 99% virtualized, even 100 %, new solutions emerge. Thus EMC has developed a solution fully virtualized CDP: RecoverPoint for Virtual Machines.
RecoverPoint: reliable, efficient and accessible
RecoverPoint for EMC VM is a virtual solution, accessible and versatile which helps restore systems at the exact time - a few microseconds - before a disaster. Amongst other features of its solution:
- • 100 % software;
- • Downloadable and 100% free (not included technical assistance);
- • 100% storage agnostic;
- • Completely independent (works with SAN, VSANs, NAS, DAS, etc.);
- • Supports all protocols (CIFS so that VVOL);
- • Allowing the orchestration of fully integrated automation vSphere Web Client.
In addition, RecoverPoint innovates by providing local protection and remote configuration as synchronous qu'asynchrone . A distinction which, despite the approach of being 100 % software, has two RecoveryPoint clusters one remote virtual environments and be synchronized on both sites.
In short, the main advantage of RecoverPoint for VM is that there is no point of potential failure, because the cluster is actually installed on two separate ESX servers.
Photo credit: © djvstock - Fotolia.com
About Blog
The right use of technology addresses business challenges and drives business growth in all areas of an enterprise. We hope this blog will offer insight into developing strategies and tactics to enable you to identify those key drivers of growth and keep pace with and anticipate the rapid technology change of today.
Posts by Topic
- IT infrastructure (118)
- IT security (95)
- IT Innovation (59)
- Trends (51)
- Cloud (48)
- Managed services (48)
- Mobility (38)
- CIO/IT leaders (29)
- Digital transformation (29)
- Events (28)
- News (23)
- Microsoft 365 (17)
- Security (17)
- IBM (16)
- Disaster recovery (DR) (14)
- High availability (12)
- Recruitment (12)
- Storage (12)
- Big Data (11)
- Collaboration (11)
- AI (10)
- Case study (9)
- Office 365 (9)
- BYOD (8)
- Customer Experience (8)
- Hybrid Cloud (7)
- Current events (6)
- SAP Hana (5)
- Business intelligence (BI) (4)
- Converged infrastructure (4)
- Convergence / Hyper-convergence (4)
- Virtualization (4)
- Copilot (3)
- Future of retail (2)
- Retail (2)
- trend (2)
- Backups (1)
- Beacon (1)
- Blog Migrations (1)
- Contests (1)
- Infrastructure TI (1)
- Innovation TI (1)
- IoT (1)
- MDM (1)
- Stockage (1)
- Virtualisation (1)
- blockchain (1)
- cio (1)
- replication (1)
- Étude de cas (1)

